Adaptive Coordination: A Doctrine Companion on Navigating the Messy Middle #
Opening: The Federation That Saved Thousands #
Before we begin, I want you to make a mental guess. In the last calendar year, how many K-12 students in the United States died in school fires? Think of the news. Think of the sheer number of schools. Got your number?
Scroll down when you are ready…
Which sounds right to you? For the whole US.
1-5 students per year?
6-10 students per year?
11-100 students per year?
101-150 students per year?
151-200 students per year?
More?!
The answer is effectively zero. It has been effectively zero since 1958.
Your guess was likely higher. Why? Because we conflate ‘danger’ with ‘outcomes.’ Fire is dangerous. But the outcome is managed. This record spans billions of student-days, making school fire safety comparable to lightning strike or shark attack risk. By some measures, it’s safer than aviation.
This extraordinary safety record didn’t emerge from centralized control. There’s no Central Bureau of Fire Drills at the National Fire Protection Association (NFPA) headquarters pressing a button for synchronized national evacuation.
Before 1958, hundreds (yes hundreds) of K-12 students died in school fires. Not because integration was attempted and failed, but because systematic coordination framework didn’t exist. Schools improvised individually. Some had plans, most didn’t. Results were tragically inconsistent.
After the Our Lady of Angels fire, NFPA developed coordination framework. Not centralized control, but federation architecture with clear protocol governance:
NFPA provides standards and guidance.
Local fire departments steward implementation at school level.
Schools adapt protocols to their buildings and practice regularly.
When alarm sounds, students execute without asking permission.
This works because:
- Framework is clear (NFPA standards)
- Stewardship relationships exist (fire department works with schools)
- Regular practice embeds protocols (fire drills become embodied knowledge)
- Accountability is distributed (each level owns their domain)
They know what to do. They’re not going to ask permission.
The Fire Alarm Test: When Framework is Absent #
Now imagine a fire alarm sounds in a shopping mall or office building right now. Be honest: would you immediately stand and evacuate, or would you look around to see what others are doing first?
Most adults look around. We wait for confirmation. We check if others are concerned. We look for authority figures to tell us what to do.
The same adults who, in K-12, executed fire drills instantly without hesitation.
What changed?
We entered environment without federation framework. The alarm “is probably just a drill” (normalcy bias) overrides any residual training. By the time we recognize it’s real, critical intervention window may have closed. Exits might be blocked, smoke spreading. The “concrete” has hardened.
The difference isn’t the people. It’s the presence or absence of coordination framework.
K-12 environment has:
- Clear protocols everyone practices
- Stewardship relationships (fire department helps schools)
- Regular rehearsal (fire drills)
- Distributed accountability (teacher leads class, principal coordinates building)
Mall/office environment has:
- No practiced protocols
- No stewardship relationships
- No rehearsal
- Unclear accountability
Same people, radically different outcomes.
Breaking the Fourth Wall: Why Binary Framing Matters #
Throughout this doctrine, I’ve presented federation and integration as distinct approaches. This binary framing is pedagogical, not absolute. Real coordination exists in messy middle, shifting across temporal, spatial, and organizational dimensions.
But without understanding the pure principles at each endpoint, practitioners have no anchor points for navigating that middle space.
Think of learning jiu-jitsu. Knowing the scissor sweep technique doesn’t mean executing it perfectly every time. It means recognizing when that’s the right move and when it needs to be abandoned. You need clear technique to recognize when context requires variation.
Similarly, understanding pure federation (coordination without authority to compel) and pure integration (unified control with authority) gives you recognition patterns for hybrid situations. Without those anchor points, you’re improvising without framework.
Key principle: Your partners have agency. You cannot predict their moves with certainty, so you need principles that guide adaptation, not scripts that prescribe execution.
This companion addresses the adaptive reality: when to shift between modes, how to recognize context signals, and why principle-based navigation beats rigid prescription.
Part 1: Two Clocks, Two Environments #
The Conference and the Tide #
Consider an academic conference. Everyone agrees presentations will be in English. Paper submissions follow conference template. But no home organization changes their internal systems to match conference standards.
This is temporary integration for bounded purpose.
The conference has no power to force organizational change. It can only set participation standards: “If you want to present here, use this template.” That’s conditional integration. You maintain autonomy, but choosing to participate means accepting standards.
What makes this work:
- Time-bound duration (annual event, then everyone returns to normal operations)
- Clear boundaries (venue standards vs home systems)
- Voluntary participation (opt-in, not mandated)
- Limited scope (presentation layer, not operational core)
The tide erases the sandcastle. Between conferences, organizations reset to their own standards. The integration doesn’t persist because it was never intended to.
When Emergency Symposia Pour Concrete #
Now imagine emergency symposia emerge mid-year. First one is justified by “crisis in the field.” Different language because key researchers can’t attend English-only event.
Second year, another emergency symposium. Now it’s “tradition.”
Third year, conference organizing committee faces reality. They now have TWO coordination regimes:
- Annual formal conference (English, established templates)
- Rolling emergency symposia (multilingual, informal standards)
The concrete resists the tide. The temporary integration assumption (annual reset) no longer holds because activity is now continuous.
Conference must either:
- Force integration: “No more emergency symposia, everything goes through annual conference” (requires authority they don’t have)
- Acknowledge federation: Invest in translation infrastructure, develop protocols for multiple coordination modes
The United Nations Pattern #
Compare to United Nations. Permanent institution invests in universal translation infrastructure. Why? Because you can’t sustain “everyone speak English” across permanent, global operations with sovereign nations.
The difference isn’t just scale. It’s temporal horizon and authority context.
Conference can set participation standards because attendance is voluntary and time-bound. UN invests in federation infrastructure because participation is permanent and sovereignty is non-negotiable.
The pattern: Temporary integration only works in constraint-based environments where checks and balances ensure reset. When exception-based environment allows ratchet moves, temporary integration becomes permanent brittleness.
Part 2: Constraint-Based vs Exception-Based Environments #
Two Clocks Operating Simultaneously #
Checks and Balances Clock (Constraint-Based, Reversible):
- Tide cycles erase sandcastles
- Court system corrects police overreach
- Annual conference cycle allows organizational reset
- Rules in handbook predict outcomes (Boy Scout mode)
- Integration works because reset is guaranteed
Ratchet Clock (Exception-Based, Irreversible):
- Concrete foundations resist tide
- Emergency authorities become normalized
- Exception symposia become permanent fixtures
- Overton window shifts what’s acceptable
- Integration assumptions break because no reset occurs
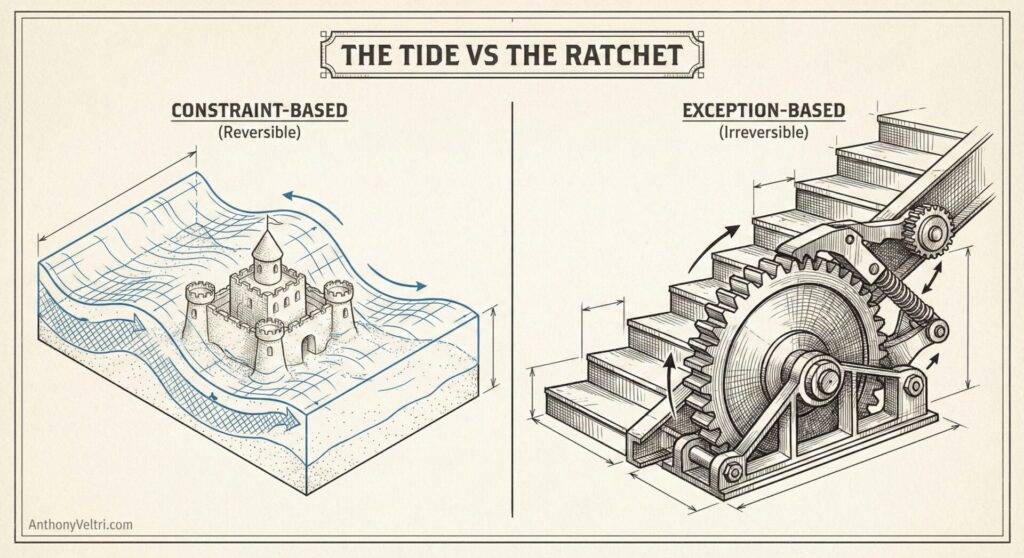
Most people who’ve spent 30+ years in their careers experienced primarily constraint-based environments. Rules predicted outcomes. Compliance worked. Temporary measures actually were temporary. The tide actually erased mistakes.
They design coordination assuming those conditions persist.
But if environment has shifted (more exceptions granted, faster ratchet moves, concrete-pouring becoming normalized), their designs fail in ways they can’t diagnose because they’re looking for constraint-based failure patterns.
The Perception Problem #
Human eyes can detect certain degrees of motion over time. If an object moves slowly enough, we literally cannot detect that motion.
This is why ratchet clock is insidious:
Slow ratchet (3 clicks per week): Perceptible, but barely, people track it.
Fast ratchet (50 clicks per week): Obviously abnormal, forces response
The danger zone (1 click per week to 2 clicks per week): Both below perception threshold
You can’t wait to SEE the ratchet operating. You have to design assuming it’s already happening.
By the time you hear the clicks, normalcy bias has already prevented intervention. The concrete hardened while you thought you were still in the constraint-based world.
Part 3: Normalcy Bias and the Fire Drill Paradox #
Why K-12 Training Doesn’t Transfer to Mall Fire Alarms #
In K-12 environment:
- Fire drills are regular, expected
- Authority structure is clear (teacher directs)
- Environment is bounded (students know the building)
- Consequences are immediate (teacher corrects mistakes)
- Constraint-based training for constraint-based environment
In mall/office environment:
- Fire alarms are rare, unexpected
- No clear authority (who’s in charge?)
- Environment is unfamiliar or unbounded
- No immediate feedback (no practiced evacuations)
- Constraint-based training fails in exception-based reality
The same coordination architect who designed successful systems in stable environment (constraint-based) looks around for authority figure when environment shifts (exception-based).
They’ve been trained for fire drills, not fires.
The Foundational Assumption #
“I am not immune to normalcy bias.”
This is the prerequisite for everything else.
You cannot update your understanding based on evidence if you don’t first acknowledge:
- You have priors (career experience in constraint-based environment)
- Those priors create blind spots (normalcy bias)
- Evidence might contradict experience (ratchet accelerating below perception)
- You need systems to compensate (Bayesian updating, instrumentation, explicit review)
Without meta-awareness, you’re the adult in the shopping mall looking around for authority while the fire spreads.
If adults who spent 12+ years practicing fire drills still succumb to normalcy bias in actual fire alarm situations, how can coordination architects who spent 30 years in constraint-based environments be expected to recognize exception-based environments without explicit awareness training?
They can’t. Unless they acknowledge normalcy bias exists and build systems to compensate.
For a thorough overview of bias and how to make better decisions, See Doctrine 22: When “It Depends” is the Right Answer
Part 4: Dimensions of Coordination Adaptation #
Real coordination rarely lives at pure endpoints. You’re constantly:
- Negotiating how much integration is necessary vs how much federation is tolerable
- Shifting between modes as context changes
- Managing tensions between partners who want different approaches
- Adapting as authority relationships evolve
The binary framework doesn’t describe reality. It provides vocabulary for navigating reality. When you can name what you’re seeing (“this is forced integration without authority to compel”), you can diagnose why it’s failing and what adjustment is needed (“shift toward federation with protocol governance”).
Temporal Dimension #
Integration may work initially when:
- Authority exists or crisis demands unified action
- Temporary coordination is needed
- Quick alignment is critical
Federation becomes necessary as:
- Autonomy increases over time
- Sustained coordination requires buy-in not compliance
- Temporary authority expires or is withdrawn
Example: NATO operations often integrate during active combat, federate during peacekeeping operations.
Spatial or Geographic Dimension #
Core operations may integrate:
- Tight coupling required
- High interdependency
- Coordination overhead acceptable for coherence gained
Peripheral operations federate:
- Loose coupling sufficient
- Autonomous execution possible
- Local knowledge matters more than central coordination
Example: Emergency management integrates at incident command post, federates across jurisdictions.
Organizational Maturity Dimension #
Young partnerships may need integration to:
- Establish shared understanding
- Build common vocabulary
- Learn each other’s capabilities
Mature partnerships can federate because:
- Protocols are established
- Trust exists
- Coordination overhead is well-understood
Example: DHS infrastructure protection evolution (iCAV started with integration push to establish standards, evolved to GII/OneView federation as components matured).
Authority Fluctuation #
Authority to compel may be:
- Granted temporarily during crisis
- Exercised during emergency operations
- Contested during recovery phase
- Withdrawn when crisis ends
Coordination approach must shift accordingly.
Example: Pandemic response integrated during emergency declaration (authority existed), needed to federate as emergency powers expired (authority withdrawn but coordination still required).
Part 5: Recognition Patterns for Mode Shifting #
Signals That Integration is Failing (Shift Toward Federation) #
Resistance increases despite authority:
- Forced compliance creates workarounds
- People follow letter of policy while violating spirit
- Energy spent on enforcement exceeds energy spent on execution
Shadow IT emerges:
- Autonomous entities develop parallel systems
- Unsanctioned tools appear because sanctioned tools don’t work
- Workarounds become normalized faster than policy can adapt
Gaming and theater:
- Partners game metrics to appear compliant
- Compliance theater (looks integrated but isn’t)
- Information withholding to maintain autonomy
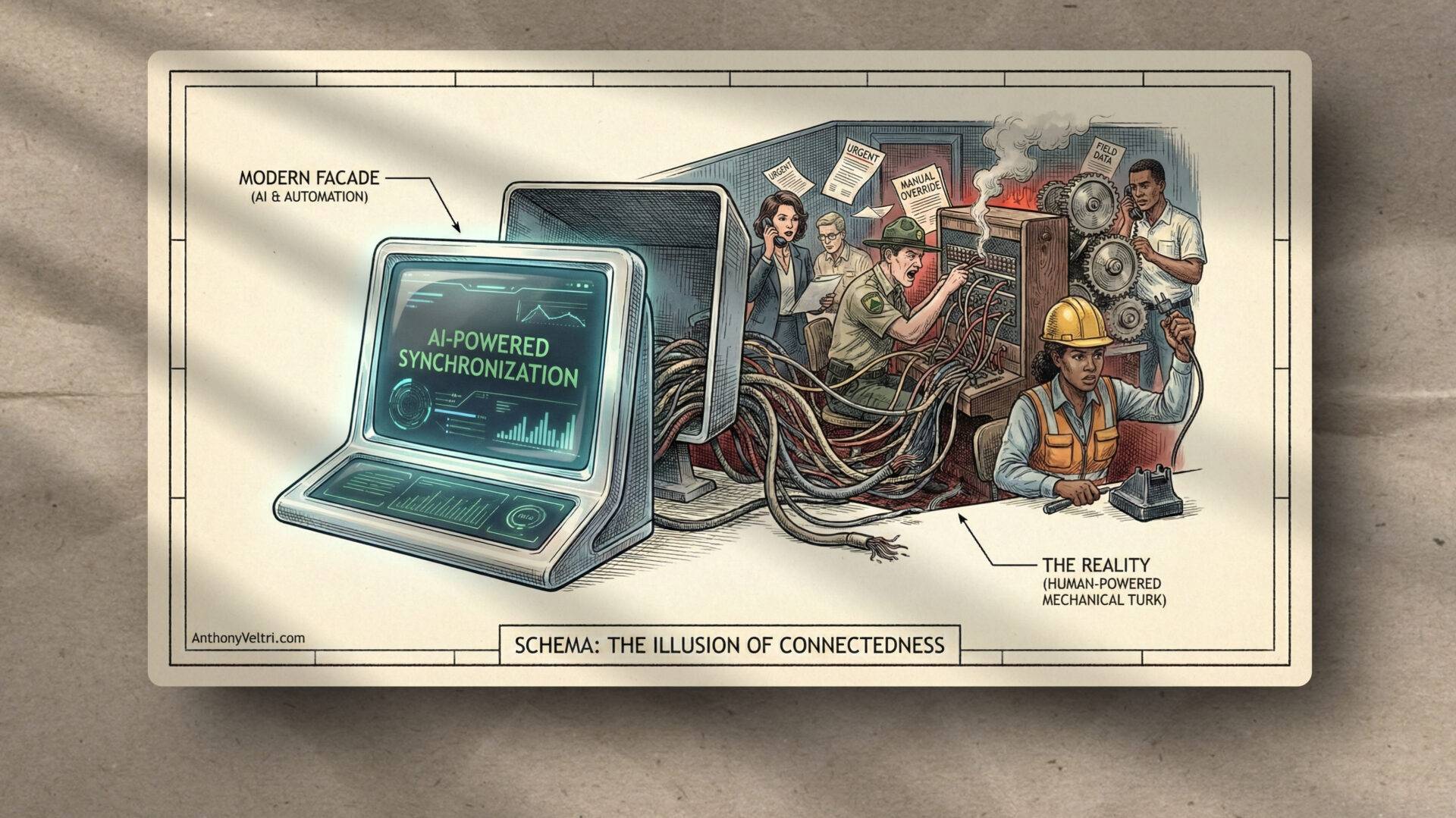
Governance doesn’t touch Shadow IT, it only impacts approved IT. By definition, governance cannot prevent workarounds because workarounds exist precisely to circumvent governance. Shadow IT is not a compliance failure; it is a design feedback signal.
Signals That Federation is Failing (Shift Toward Integration) #
Coordination failures create unacceptable risk:
- Lives at stake
- Security compromised
- Mission failure imminent
Temporary authority becomes available:
- Crisis declaration
- Funding mandate
- Political alignment creates window
Partners request more structure:
- Coordination overhead exceeds execution time
- Incompatible implementations prevent interoperability
- Each entity optimizing locally creates global dysfunction
Common threat creates alignment:
- External pressure forces cooperation
- Partners recognize coordination cost is worth bearing
- Integration becomes preferable to federation overhead
Part 6: Hybrid Architectures (Integration Core, Federation Periphery) #
Some systems succeed by combining modes strategically.
The Pattern #
Integrate:
- Core data standards
- Critical interoperability requirements
- Safety protocols
- Security baselines
Federate:
- Implementation approaches
- User interfaces
- Local adaptations
- Operational processes
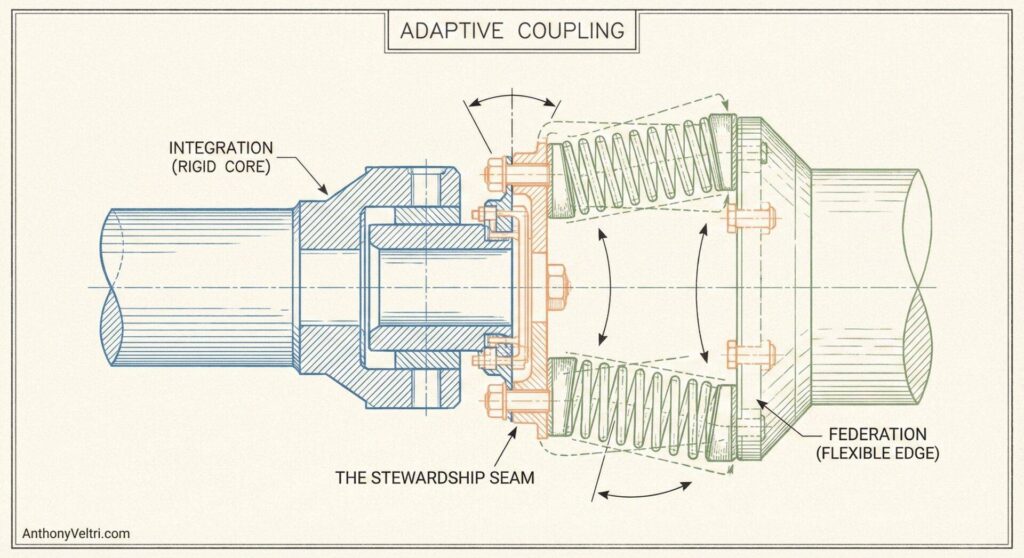
Why This Works #
Integration provides coherence where it matters most.
Everyone speaks same core language, critical systems can interoperate.
Federation provides flexibility where local knowledge matters.
Implementation details vary based on context, users adapt to local needs.
Clear boundaries between integrated and federated domains.
Everyone knows what must be standardized vs what can vary.
Example: DHS Infrastructure Protection #
Integrated: Data model, core taxonomy, security standards
Federated: Adoption across 22 DHS components, implementation timelines, user training
This worked because:
- Integration scope was minimal (just enough to interoperate)
- Federation allowed components to maintain sovereignty
- Boundaries were explicit (what integrates vs what federates)
- Stewardship existed (not just mandates)
When Hybrid Architecture Fails #
Boundary drawn wrong:
- Too much integration (creates brittleness, invites workarounds)
- Too little integration (coordination fails, incompatibility)
- Unclear boundaries (confusion about what’s standardized)
No stewardship at interface:
- Integration mandated without support
- Federation assumed without protocols
- Boundary maintenance neglected
Part 7: The Bayesian Assessment Framework #
Your Career Gave You “Priors” #
If you spent 30 years in a constraint-based environment, you carry a specific mental map of how the world works:
- Rules predict outcomes.
- Temporary measures are actually temporary.
- Governance can see everything.
These assumptions aren’t “wrong.” They were accurate for the world you used to live in. In statistics, these are called your priors—the baseline beliefs you hold before you see new data.
The Trap of the Expert The problem isn’t that you are ignoring the evidence. The problem is that your “priors” are so strong that they overpower the evidence. When you see a “ratchet move” (a temporary measure becoming permanent), your mental map dismisses it as an anomaly rather than a new pattern. To survive the messy middle, you need a system for updating that map.
Evidence to Update On #
Exception frequency increasing:
- “Temporary” measures not sunsetting
- Emergency authorities becoming normalized
- Exceptions cited more frequently than rules
Shadow IT emerging:
- Parallel systems appearing
- Workarounds developing faster than policy adapts
- Unsanctioned coordination becoming normalized
Governance losing visibility:
- Can’t see all coordination activity
- Enforcement becoming arbitrary (can’t catch all violations)
- Policy compliance declining despite increased enforcement
Integration brittleness:
- Resistance increasing despite authority
- More energy spent on enforcement than execution
- Partners developing workarounds
The Update Mechanism #
Prior: “I’m operating in constraint-based environment” (career experience)
Evidence: Exception patterns, Shadow IT emergence, governance gaps
Updated belief: “I’m operating in exception-based environment (or hybrid with significant exception-based components)”
Design implication: Don’t design integration assuming tide will erase mistakes. Design federation assuming concrete will get poured.
The Intervention Timing Problem #
You can’t wait to detect ratchet clock operating. By the time clicks are audible, concrete has already hardened.
You need instrumentation:
- Measure exception frequency over time
- Track Shadow IT emergence patterns
- Monitor governance visibility gaps
- Assess enforcement consistency
You can’t rely on human perception because ratchet acceleration from 1 click per week to 2 clicks per week operates below perception threshold.
Both rates are slow enough to seem normal. But doubling rate is critical signal that environment is shifting.
Part 8: Design Principles for Adaptive Coordination #
Principle 1: Assess Environment Type Before Designing #
Don’t assume constraint-based just because that’s career experience.
Ask diagnostic questions:
- How frequently are exceptions granted?
- Do temporary measures sunset or become normalized?
- Can governance see all coordination activity?
- Is enforcement consistent or arbitrary?
- Do workarounds emerge faster than policy adapts?
If evidence points to exception-based environment, design for federation even if integration seems “easier.”
Principle 2: Build Reset Mechanisms into Integration #
If you must integrate temporarily:
Explicit sunset provisions: Authority expires on date certain, not “when crisis ends”
Exception monitoring: Track how often exceptions granted, watch for normalization
Governance visibility: Make Shadow IT observable (can’t manage what you can’t see)
Regular assessment: Review whether integration assumptions still hold
“The tide will erase this” only works if you actually schedule the tide.
Principle 3: Design Assuming Concrete Will Get Poured #
Assume:
- Exceptions will be granted
- Temporary will become permanent
- Workarounds will emerge
- Parallel systems will develop
Then ask: “If concrete gets poured, does the architecture still function?”
If answer is “no, integration becomes brittle,” choose federation from start.
Principle 4: Instrument for Imperceptible Drift #
Since humans can’t perceive slow ratchet acceleration:
Create measurement systems:
- Exception frequency over time
- Time between “emergency” events
- Shadow IT emergence patterns
- Governance visibility metrics
Build redundant monitoring:
- Multiple detection mechanisms
- Cross-validation of signals
- Regular explicit review points
You can’t rely on perception. You need measurement systems that detect imperceptible drift.
Principle 5: Anticipatory Intervention, Not Reactive Response #
You can’t wait to see the problem.
Fire alarm in mall: If you wait to see others evacuating before you move, you’ve already lost critical seconds.
Ratchet clock: If you wait to hear clicks before designing for exception-based environment, concrete has already hardened.
Design must be anticipatory:
- Assume exception-based components present
- Build federation capabilities before you need them
- Establish stewardship relationships early
- Practice protocols before crisis
Part 9: Protocol Governance (The NFPA Model) #
The fire drill success reveals what makes federation work at scale.
Three Levels of Stewardship #
NFPA (Framework Level):
- Develops fire safety standards
- Updates based on lessons learned
- Provides guidance and training materials
- No direct control over individual schools
Local Fire Department (Stewardship Level):
- Helps coordinate school fire drills
- Provides expertise on local conditions
- Builds relationship with schools
- Inspects facilities
- They’re stewarding the protocol, not commanding execution
Individual Schools (Execution Level):
- Adapt framework to building layout
- Practice protocols regularly
- Execute during actual emergencies
- Maintain accountability systems
- They know what to do, they’re not going to ask permission
Why This Works #
Framework is clear but not prescriptive (principles, not mandates)
Stewardship relationships exist at interfaces (fire department works with schools)
Regular practice embeds protocols (fire drills create embodied knowledge)
Accountability is distributed (each level owns their domain)
Autonomy with coordination (schools execute independently but within framework)
What Protocol Governance Requires #
Investment in framework development:
- Someone must maintain standards (NFPA role)
- Updates based on lessons learned
- Training materials and guidance
- This is stewardship work, not enforcement
Interface stewardship:
- Someone operates at boundary (fire department role)
- Translates framework to local context
- Builds relationships with executors
- Provides expertise without commanding
- This enables coordination without authority
Regular practice:
- Protocols must be rehearsed
- Can’t just exist on paper
- Must become embodied knowledge
- Fire drills work because they’re practiced, not just documented
Federation Requires Different Investment Than Integration #
Integration invests in:
- Enforcement infrastructure
- Compliance monitoring
- Centralized control systems
- Mandate authority
Federation invests in:
- Framework development
- Stewardship relationships
- Protocol governance
- Practice and rehearsal
Different cost structures, different capabilities, different failure modes.
The Thermodynamics of Coordination (The Energy Hill) #
There is a fundamental energy asymmetry between these two modes that most budgets ignore.
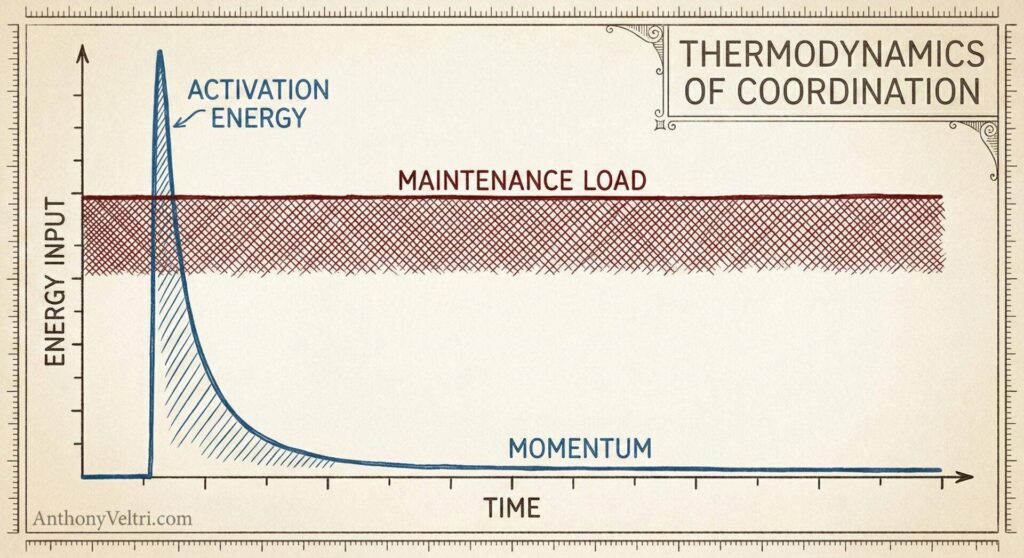
Integration acts against entropy. It tries to keep distinct, autonomous entities bound together in a way they wouldn’t naturally arrange themselves.
- The Physics: It is like holding a beach ball underwater. It requires Constant Energy Input (enforcement, compliance checks, manual reconciliation).
- The Cost: If you stop spending energy (cut the budget, remove the mandate), the system immediately snaps back to its natural state (fragmentation).
- The Trap: It looks cheaper upfront because you skip the messy negotiation phase, but the “operating cost” is infinite because you are fighting gravity forever.
Federation works with entropy. It accepts that entities want to be autonomous and builds channels for them to flow in alignment.
- The Physics: It is like digging an irrigation canal. It requires Massive Activation Energy (negotiating protocols, building the framework, training the stewards).
- The Cost: This is expensive and slow at the start. But once the canal is dug and the water (autonomy) is flowing, the Maintenance Energy is low. Gravity does the work.
- The Payoff: If you step away, the system continues to function because the behavior is embodied, not enforced.
The Budget Mistake: Leaders choose Integration because it has lower Activation Energy (“Just mandate it!”), ignoring that it has infinite Maintenance Energy. They avoid Federation because the Activation Energy is high (“This is taking too long!”), missing that it creates a durable asset that runs on its own momentum.
Part 10: Resistance Patterns and Root Depth #
When coordination fails, it manifests in three patterns. Each has different visibility and different depth of roots.
Pattern 1: Catastrophic Failure (Visible, Forces Response) #
Coordination stops functioning completely.
Characteristics:
- Obvious to everyone
- Creates forcing function to redesign
- Can’t be ignored
- Fast ratchet (50 clicks per week)
Example: System crashes, mission fails, safety incident occurs
Why this is “easiest” to address:
- Failure is undeniable
- Creates urgency for change
- Resources mobilize
- Authority to redesign emerges
Pattern 2: Semi-Sanctioned Shadow IT (Chronic, Grows Roots) #
Coordination sort of works, but through unofficial channels.
Characteristics:
- Parallel systems gain legitimacy without official acknowledgment
- Deeper roots because it’s “working well enough”
- No forcing function because it hasn’t fully broken
- Slow ratchet acceleration (imperceptible)
Example: Everyone uses unsanctioned tool, IT pretends not to notice, workaround becomes normalized
Why this is more dangerous:
- No crisis to force attention
- Appears to be functioning
- Alternative would require admitting official approach failed
- Roots grow deeper while everyone pretends it’s temporary
Pattern 3: Official Denial (Deepest Roots, Prevents Recognition) #
Official narrative persists despite reality.
Characteristics:
- Policy says one thing, practice does another
- Emergency symposia keep happening but aren’t acknowledged in governance
- Coordination works through informal channels while formal structure ossifies
- Deepest roots because official story prevents addressing reality
Example: Annual conference policy remains “English only” while emergency symposia operate multilingually, no governance acknowledgment of parallel structure
Why this is most dangerous:
- Normalcy bias intact
- Can’t address problem you won’t acknowledge
- Formal structure becomes theater
- Real coordination happens in shadows
- No path to improvement because problem is denied
The Fire Alarm Parallel #
Catastrophic failure: Building obviously on fire, everyone evacuates immediately
Semi-sanctioned workaround: People notice alarm but check with others first, create informal evacuation without official protocol
Official denial: People hear alarm, assume it’s “probably just a drill,” continue normal activities while fire spreads
Looking around while building burns.
Why Chronic Dysfunction is More Dangerous Than Acute Failure #
Acute failure creates obvious symptoms that force treatment.
Chronic dysfunction slowly undermines while maintaining appearance of function.
By the time chronic becomes acute (Shadow IT creates security breach, parallel coordination fails catastrophically, denied problem becomes undeniable), roots are so deep that redesign is far more painful than if addressed early.
But early intervention requires acknowledging normalcy bias and updating priors based on evidence rather than experience.
Part 11: Domain Applications #
DHS Infrastructure Protection Evolution #
Early 2000s (No Framework):
- Each DHS component operated independently
- Some had infrastructure protection programs, most didn’t
- Inconsistent approaches, gaps in coverage
- No systematic coordination
iCAV Integration Phase:
- Attempted to establish common approach
- Provided tools and standards
- Required components to participate
- Integration worked initially to establish shared understanding
GII/OneView Federation Phase:
- Components matured, developed local capabilities
- Integration became brittle (components developing workarounds, exclusion of external partners who couldn’t meet integration standards)
- Shifted to federation model
- Provided framework, components adapted to local needs
- 296,000+ users across 22 DHS components
Why the shift worked:
- Recognized integration assumptions breaking down
- Acknowledged components had developed autonomy
- Invested in federation infrastructure (protocols, interfaces)
- Maintained stewardship relationships
What would have failed:
- Continuing to enforce integration despite resistance
- Denying that Shadow IT was emerging
- Assuming temporary integration could be sustained indefinitely
Coalition Operations (Emergency Authorities That Don’t Sunset) #
Crisis Phase:
- Coalition forms in response to threat
- Emergency authorities granted
- Integration works (unified command, shared resources)
- Temporary authority enables temporary integration
Extended Operations:
- Crisis extends beyond initial timeline
- Emergency authorities “temporary” extension becomes normalized
- Partners expect sunset, authority persists
- Integration designed for temporary use becomes permanent
Post-Crisis:
- Threat diminishes but coalition persists
- Authority supposed to be withdrawn never is
- Partners increasingly resistant to integration
- Brittle structure, Shadow IT emerging
What shift requires:
- Acknowledge operation is now sustained, not temporary
- Invest in federation infrastructure
- Transition from emergency authority to protocol governance
- Rebuild for permanence, not extended temporariness
Enterprise Architecture (Temporary Workarounds Become Permanent) #
“We’ll use this temporarily until new system launches”:
- Temporary database for migration
- Interim reporting tool
- Emergency access workaround
- Integration assumed these would sunset
Six months later:
- New system delayed
- Temporary tools now mission-critical
- People built processes around workarounds
- Concrete poured, tide can’t erase
Two years later:
- “Temporary” is permanent
- Official architecture pretends these don’t exist
- Shadow IT normalized
- Can’t redesign without acknowledging reality
What recovery requires:
- Acknowledge temporary became permanent
- Either formalize (bring into governance) or replace (invest in real solution)
- Stop pretending tide will erase concrete that’s already hardened
Part 12: When Binary Thinking Becomes Dangerous #
Integration Absolutism #
“If we just had more authority, this would work.”
The trap:
- Ignores that authority to compel may be politically or organizationally impossible
- Leads to continued investment in failing approach
- Blames “lack of compliance” rather than flawed design
- Assumes problem is execution, not architecture
Reality:
- Authority you don’t have can’t be assumed
- Forcing integration without authority creates Shadow IT
- More enforcement creates more sophisticated workarounds
Federation Romanticism #
“Autonomous coordination always produces better outcomes.”
The trap:
- Ignores contexts where integration is necessary (safety, security, crisis)
- Leads to coordination failures that create harm
- Assumes all partners have capability for autonomous execution
- Romantic about self-organization without acknowledging overhead
Reality:
- Some contexts require integration (emergency response, safety protocols)
- Federation has coordination overhead that can exceed integration cost
- Not all partners have maturity for autonomous operation
The Principle: Match Approach to Context, Not Ideology #
Integration works when:
- Authority to compel exists
- Temporary coordination needed
- Safety/security requires standardization
- Partners lack capability for autonomy
Federation works when:
- Authority to compel is absent or unreliable
- Sustained coordination required
- Local knowledge matters more than central control
- Partners have capability for autonomous execution
Hybrid works when:
- Clear boundaries can be drawn
- Some domains require integration, others federation
- Stewardship relationships can manage interfaces
The failure mode is choosing your architecture based on your ideology rather than your reality.
Closing: Anchor Points for Navigating the Messy Middle #
I developed federation vs integration as binary distinction because that’s how I needed to understand my field failures. Why did forced integration keep producing Shadow IT? Because we lacked authority to compel, but acted like we had it.
The binary helped me see the pattern.
But operational success requires:
- Knowing when to shift between modes
- Recognizing when to combine them
- Updating as context changes enough to reconsider approach
These frameworks are anchor points, not destinations.
The fire drill works because framework plus stewardship plus autonomy produces reliable coordination at massive scale. Not because federation is ideologically superior, but because it matches the coordination reality: thousands of autonomous entities who can’t be centrally commanded but can execute protocols when properly stewarded.
The mall fire alarm fails because framework is absent. Same people, different outcome based on infrastructure presence.
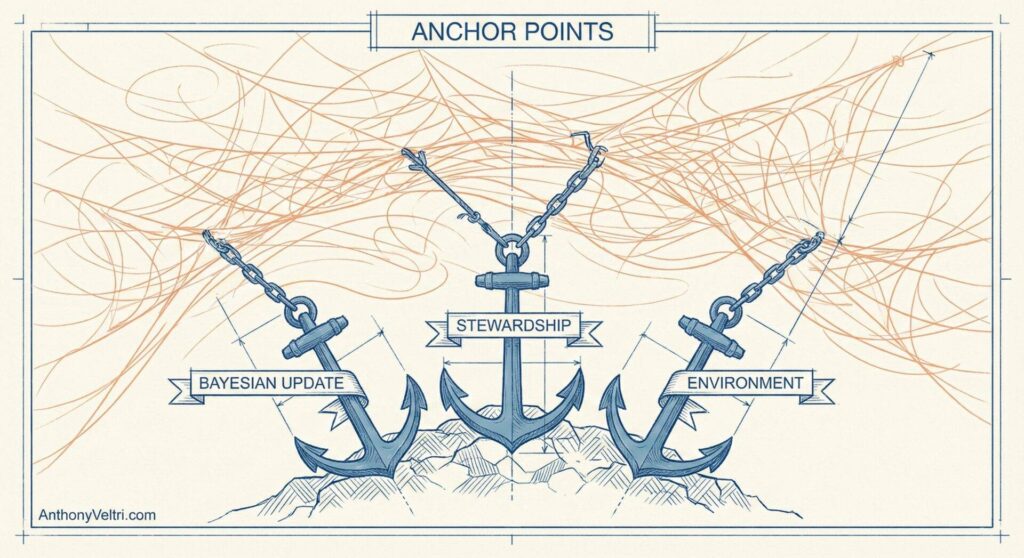
Your task as coordination architect:
Assess environment honestly (constraint-based or exception-based?)
Acknowledge normalcy bias (are you designing for world you experienced or world you’re operating in?)
Choose approach that matches context (not ideology or preference)
Build appropriate infrastructure (enforcement for integration, stewardship for federation)
Instrument for imperceptible drift (you can’t rely on perception)
Update priors based on evidence (Bayesian assessment, not career assumptions)
The messy middle is where you’ll spend your career.
These anchor points give you vocabulary to navigate it with principle-based judgment rather than rigid prescription or improvised guesswork.
Use them well.
Field notes and examples #
Last Updated on February 22, 2026